Data Privacy & Encrypted Visitor Management
Secure, compliant visitor management.
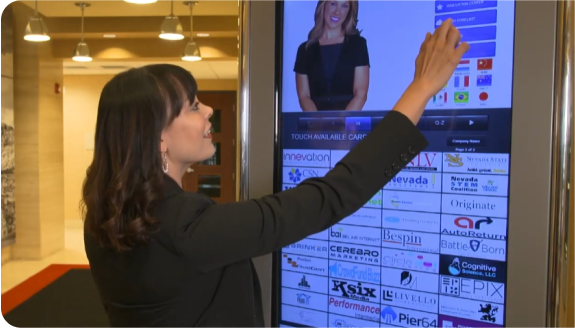
ALICE Receptionist visitor management systems take data privacy and encryption seriously, protecting visitor details while delivering a professional experience.
The Risk of Unsecured Visitor Data
Visitor data isn’t just a sign-in record — it’s sensitive information. When names, contact details, and visit reasons are stored in paper logs or outdated systems, they become security and compliance risks.
Unsecured sign-in processes expose visitor details, create audit gaps, and are inefficient. IT and security leaders need a visitor management system that closes these gaps instead of creating new ones.

A Visitor Management System Built for Data Privacy
ALICE Receptionist is built for organizations that treat data privacy as non-negotiable. Collect only the visitor data you need, protect it with secure handling, and enforce consistent retention rules across every location.
With encrypted visitor data and customizable retention policies, ALICE secures your lobby while giving guests a fast, professional, frictionless check-in experience.

SOC 2 Type II Certified for Secure Visitor Management
ALICE Receptionist is SOC 2 Type II certified by the AICPA, demonstrating our commitment to protecting visitor data through rigorous security, availability, and confidentiality controls. Organizations that prioritize data privacy trust ALICE for secure, compliant, and auditable visitor management.
ALICE Receptionist Delivers Data Privacy and Visitor Management End-to-End
Privacy by Design
ALICE Receptionist standardizes how visitor data is collected, stored, and accessed across your organization.
Define consistent check-in flows, consent language, and data fields so every visitor interaction aligns with your security and data privacy policies and supports a safe, secure workplace.
Encrypted Visitor Data
ALICE protects visitor data using Microsoft Azure’s built-in security platform. Azure encrypts data at rest with AES-256 and secures data in transit with modern TLS protocols, helping you deliver encrypted visitor management from check-in to data retention.
Custom Data Retention Policies
Every organization has different requirements for how long visitor data should be kept. ALICE Receptionist supports custom data retention policies, so you can align with internal policies, contractual obligations, and data privacy regulations.
Centralized Visibility & Access Control
ALICE gives IT and security teams a single source of truth for visitor activity, with audit-ready records and role-based access to control who can view or export data.
“I would highly recommend the ALICE system because we were able to accomplish what we wanted to do and it works perfectly. We’re a highly technical facility and reception is one of the tasks that we’ve automated. It’s been great to have been able to do this.”
– Mike Van Meerten, IT Director, Meissner Filtration Products, Inc.
Elevated Visitor Data Privacy and Visitor Management for Your Industry
Book a Demo
Get a Personalized Demo of Secure, Encrypted Visitor Management
See how ALICE Receptionist helps your organization protect visitor data, meet SOC 2–level expectations, and streamline lobby operations using Azure-based encryption, custom data retention policies, and centralized visitor management controls.
Select a date to schedule your personalized demo.
Companies That Trust ALICE Receptionist for Secure Visitor Management
Frequently Asked Questions
ALICE Receptionist combines a professional first impression with strong data governance and security practices. Create consistent, automated check-in workflows while encrypting visitor data in transit and at rest. Enforce custom data retention policies and apply role-based access to visitor information, giving IT and security teams the control they need over visitor data privacy.
Yes. ALICE Receptionist is built to meet SOC 2–level security, availability, and confidentiality standards and is designed for organizations that prioritize data privacy. Running on Microsoft Azure, the platform supports encrypted visitor data, access controls, and structured audit trails to help your IT and security teams manage risk and demonstrate good data stewardship.
ALICE is designed to protect visitor data using encryption in transit and at rest, following industry-standard security practices.
Data in transit is encrypted using modern TLS protocols (typically TLS 1.2 or higher) between ALICE devices, services, and administrative dashboards. Data at rest is encrypted using strong encryption algorithms such as AES-256 through Microsoft Azure’s platform-level protections.
Yes. ALICE Receptionist supports custom data retention policies so you can define how long visitor records are stored. This helps you comply with internal policies and privacy regulations while reducing the risk of holding onto data longer than necessary.
Yes. You can manage visitor workflows, retention rules, and access controls across multiple offices from a single dashboard. This gives IT and security teams centralized visibility while ensuring that each location follows consistent standards for visitor data privacy and security.
Access to visitor records across different locations is controlled using role-based permissions. Administrators can define which team members can view, manage, or export visitor information, helping ensure that only authorized staff can access sensitive data and that every action is more easily auditable.